type
Post
status
Published
date
Feb 28, 2023
slug
SM3&SM4
summary
python SM3&SM4
tags
Crypto
category
CRYPTO
icon
password
SM4
from tqdm import tqdm class SM4(): def __init__(self,m,key): self.m=m self.key=key self.S=[ [0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x05], [0x2b, 0x67, 0x9a, 0x76, 0x2a, 0xbe, 0x04, 0xc3, 0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99], [0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef, 0x98, 0x7a, 0x33, 0x54, 0x0b, 0x43, 0xed, 0xcf, 0xac, 0x62], [0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x08, 0xe8, 0x95, 0x80, 0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6], [0x47, 0x07, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19, 0xe6, 0x85, 0x4f, 0xa8], [0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0x0f, 0x4b, 0x70, 0x56, 0x9d, 0x35], [0x1e, 0x24, 0x0e, 0x5e, 0x63, 0x58, 0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x01, 0x21, 0x78, 0x87], [0xd4, 0x00, 0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c, 0x36, 0x02, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e], [0xea, 0xbf, 0x8a, 0xd2, 0x40, 0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1], [0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55, 0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3], [0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23, 0xab, 0x0d, 0x53, 0x4e, 0x6f], [0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x03, 0xff, 0x6a, 0x72, 0x6d, 0x6c, 0x5b, 0x51], [0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8], [0x0a, 0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd, 0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0], [0x89, 0x69, 0x97, 0x4a, 0x0c, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1, 0x09, 0xc5, 0x6e, 0xc6, 0x84], [0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d, 0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48]] self.FK = [0xA3B1BAC6, 0x56AA3350, 0x677D9197, 0xB27022DC] self.CK = [0x00070e15, 0x1c232a31, 0x383f464d, 0x545b6269, 0x70777e85, 0x8c939aa1, 0xa8afb6bd, 0xc4cbd2d9, 0xe0e7eef5, 0xfc030a11, 0x181f262d, 0x343b4249, 0x50575e65, 0x6c737a81, 0x888f969d, 0xa4abb2b9, 0xc0c7ced5, 0xdce3eaf1, 0xf8ff060d, 0x141b2229, 0x30373e45, 0x4c535a61, 0x686f767d, 0x848b9299, 0xa0a7aeb5, 0xbcc3cad1, 0xd8dfe6ed, 0xf4fb0209, 0x10171e25, 0x2c333a41, 0x484f565d, 0x646b7279] def cl(self,A, x): return ((A << x) | (A >> (32 - x))) & 0xffffffff def t(self,A): a=self.S[int(A[0],16)][int(A[1],16)] b=self.S[int(A[2],16)][int(A[3],16)] c=self.S[int(A[4],16)][int(A[5],16)] d=self.S[int(A[6],16)][int(A[7],16)] #print(hex(a),hex(b),hex(c),hex(d)) return int(hex(a)[2:].zfill(2)+hex(b)[2:].zfill(2)+hex(c)[2:].zfill(2)+hex(d)[2:].zfill(2),16) def L(self,B): return (B^self.cl(B,2)^self.cl(B,10)^self.cl(B,18)^self.cl(B,24))&0xffffffff def L_(self,B): return (B^self.cl(B,13)^self.cl(B,23))&0xffffffff def T(self,A,x): A=hex(A)[2:].zfill(8) if x==0: return self.L(self.t(A)) else: return self.L_(self.t(A)) def key_expand(self): mk0 = int(self.key[:8],16) mk1 = int(self.key[8:16],16) mk2 = int(self.key[16:24],16) mk3 = int(self.key[24:32],16) k0 = mk0^self.FK[0] k1 = mk1^self.FK[1] k2 = mk2 ^ self.FK[2] k3 = mk3 ^ self.FK[3] rk=[] for i in range(32): rk.append(k0^self.T(k1^k2^k3^self.CK[i],1)) k0=k1 k1=k2 k2=k3 k3=rk[i] #print(hex(rk[i])[2:]) #input() return rk def encrypt(self): rk = self.key_expand() x0 = int(self.m[:8],16) x1 = int(self.m[8:16],16) x2 = int(self.m[16:24],16) x3 = int(self.m[24:32],16) for i in range(32): xx=x0^self.T(x1^x2^x3^rk[i],0) x0=x1 x1=x2 x2=x3 x3=xx self.m=hex(x3)[2:].zfill(8)+hex(x2)[2:].zfill(8)+hex(x1)[2:].zfill(8)+hex(x0)[2:].zfill(8) return self.m def decrypt(self): rk = self.key_expand()[::-1] x0 = int(self.m[:8],16) x1 = int(self.m[8:16],16) x2 = int(self.m[16:24],16) x3 = int(self.m[24:32],16) for i in range(32): xx=x0^self.T(x1^x2^x3^rk[i],0) x0=x1 x1=x2 x2=x3 x3=xx self.m=hex(x3)[2:].zfill(8)+hex(x2)[2:].zfill(8)+hex(x1)[2:].zfill(8)+hex(x0)[2:].zfill(8) return self.m m='0123456789abcdeffedcba9876543210' key='0123456789abcdeffedcba9876543210' sm4=SM4(m,key) # print(sm4.encrypt()) # print(sm4.decrypt()) for i in tqdm(range(1000000)): sm4.encrypt() print(sm4.m)
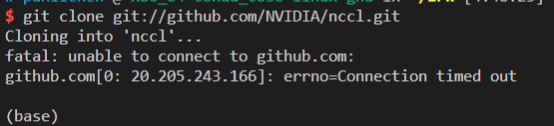
短学期第一天把SM4搞出来了 跟着文档搞 出错的点一个是 循环左移,之前都是直接左移的,没注意到 另一个就是非线性变换函数的应用。
信息安全工程课重新搞了一下嗷嗷
SM4
from tqdm import tqdm class SM4(): def __init__(self,m,key): self.m=m self.key=key self.S=[ [0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x05], [0x2b, 0x67, 0x9a, 0x76, 0x2a, 0xbe, 0x04, 0xc3, 0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99], [0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef, 0x98, 0x7a, 0x33, 0x54, 0x0b, 0x43, 0xed, 0xcf, 0xac, 0x62], [0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x08, 0xe8, 0x95, 0x80, 0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6], [0x47, 0x07, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19, 0xe6, 0x85, 0x4f, 0xa8], [0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0x0f, 0x4b, 0x70, 0x56, 0x9d, 0x35], [0x1e, 0x24, 0x0e, 0x5e, 0x63, 0x58, 0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x01, 0x21, 0x78, 0x87], [0xd4, 0x00, 0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c, 0x36, 0x02, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e], [0xea, 0xbf, 0x8a, 0xd2, 0x40, 0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1], [0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55, 0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3], [0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23, 0xab, 0x0d, 0x53, 0x4e, 0x6f], [0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x03, 0xff, 0x6a, 0x72, 0x6d, 0x6c, 0x5b, 0x51], [0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8], [0x0a, 0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd, 0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0], [0x89, 0x69, 0x97, 0x4a, 0x0c, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1, 0x09, 0xc5, 0x6e, 0xc6, 0x84], [0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d, 0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48]] self.FK = [0xA3B1BAC6, 0x56AA3350, 0x677D9197, 0xB27022DC] self.CK = [0x00070e15, 0x1c232a31, 0x383f464d, 0x545b6269, 0x70777e85, 0x8c939aa1, 0xa8afb6bd, 0xc4cbd2d9, 0xe0e7eef5, 0xfc030a11, 0x181f262d, 0x343b4249, 0x50575e65, 0x6c737a81, 0x888f969d, 0xa4abb2b9, 0xc0c7ced5, 0xdce3eaf1, 0xf8ff060d, 0x141b2229, 0x30373e45, 0x4c535a61, 0x686f767d, 0x848b9299, 0xa0a7aeb5, 0xbcc3cad1, 0xd8dfe6ed, 0xf4fb0209, 0x10171e25, 0x2c333a41, 0x484f565d, 0x646b7279] def cl(self,A, x): return ((A << x) | (A >> (32 - x))) & 0xffffffff def t(self,A): a=self.S[int(A[0],16)][int(A[1],16)] b=self.S[int(A[2],16)][int(A[3],16)] c=self.S[int(A[4],16)][int(A[5],16)] d=self.S[int(A[6],16)][int(A[7],16)] #print(hex(a),hex(b),hex(c),hex(d)) return int(hex(a)[2:].zfill(2)+hex(b)[2:].zfill(2)+hex(c)[2:].zfill(2)+hex(d)[2:].zfill(2),16) def L(self,B): return (B^self.cl(B,2)^self.cl(B,10)^self.cl(B,18)^self.cl(B,24))&0xffffffff def L_(self,B): return (B^self.cl(B,13)^self.cl(B,23))&0xffffffff def T(self,A,x): A=hex(A)[2:].zfill(8) if x==0: return self.L(self.t(A)) else: return self.L_(self.t(A)) def key_expand(self): mk0 = int(self.key[:8],16) mk1 = int(self.key[8:16],16) mk2 = int(self.key[16:24],16) mk3 = int(self.key[24:32],16) k0 = mk0^self.FK[0] k1 = mk1^self.FK[1] k2 = mk2 ^ self.FK[2] k3 = mk3 ^ self.FK[3] rk=[] for i in range(32): rk.append(k0^self.T(k1^k2^k3^self.CK[i],1)) k0=k1 k1=k2 k2=k3 k3=rk[i] #print(hex(rk[i])[2:]) #input() return rk def encrypt(self): rk = self.key_expand() x0 = int(self.m[:8],16) x1 = int(self.m[8:16],16) x2 = int(self.m[16:24],16) x3 = int(self.m[24:32],16) for i in range(32): xx=x0^self.T(x1^x2^x3^rk[i],0) x0=x1 x1=x2 x2=x3 x3=xx self.m=hex(x3)[2:].zfill(8)+hex(x2)[2:].zfill(8)+hex(x1)[2:].zfill(8)+hex(x0)[2:].zfill(8) return self.m def decrypt(self): rk = self.key_expand()[::-1] x0 = int(self.m[:8],16) x1 = int(self.m[8:16],16) x2 = int(self.m[16:24],16) x3 = int(self.m[24:32],16) for i in range(32): xx=x0^self.T(x1^x2^x3^rk[i],0) x0=x1 x1=x2 x2=x3 x3=xx self.m=hex(x3)[2:].zfill(8)+hex(x2)[2:].zfill(8)+hex(x1)[2:].zfill(8)+hex(x0)[2:].zfill(8) return self.m m='0123456789abcdeffedcba9876543210' key='0123456789abcdeffedcba9876543210' sm4=SM4(m,key) # print(sm4.encrypt()) # print(sm4.decrypt()) for i in tqdm(range(1000000)): sm4.encrypt() print(sm4.m)
SM3
class SM3(): def __init__(self, m, iv): self.iv = iv self.m = m def cl(self,A, x): return ((A << x) | (A >> (32 - x))) & 0xffffffff def FF(self,X, Y, Z, j): if j < 16: return X ^ Y ^ Z else: return (X & Y) | (X & Z) | (Y & Z) def GG(self,X, Y, Z, j): if j < 16: return X ^ Y ^ Z else: return (X & Y) | (~X & Z) # 填充 def pad(self,m): a = '' for i in m: a += bin(ord(i))[2:].zfill(8) lenth = len(a) a += '1' k = 448 - (lenth + 1) % 512 a += '0' * k a += bin(lenth)[2:].zfill(64) return a # 置换函数 def P(self,x, n): if n == 0: return x ^ self.cl(x, 9) ^ self.cl(x, 17) elif n == 1: return x ^ self.cl(x, 15) ^ self.cl(x, 23) # 压缩函数 def CF(self,V, b): A = int(V[:8], 16) B = int(V[8:8 * 2], 16) C = int(V[8 * 2:8 * 3], 16) D = int(V[8 * 3:8 * 4], 16) E = int(V[8 * 4:8 * 5], 16) F = int(V[8 * 5:8 * 6], 16) G = int(V[8 * 6:8 * 7], 16) H = int(V[56:64], 16) for j in range(64): # print(hex(A)[2:], hex(B)[2:], hex(C)[2:], hex(D)[2:], hex(E)[2:],hex(F)[2:],hex(G)[2:],hex(H)[2:]) if (j < 16): SS1 = self.cl((self.cl(A, 12) + E + self.cl(0x79cc4519, j % 32)) & 0xffffffff, 7) else: SS1 = self.cl((self.cl(A, 12) + E + self.cl(0x7a879d8a, j % 32)) & 0xffffffff, 7) SS2 = SS1 ^ self.cl(A, 12) TT1 = (self.FF(A, B, C, j) + D + SS2 + b[68 + j]) % 2 ** 32 TT2 = (self.GG(E, F, G, j) + H + SS1 + b[j]) % 2 ** 32 D = C C = self.cl(B, 9) B = A A = TT1 H = G G = self.cl(F, 19) F = E E = self.P(TT2, 0) # print(hex(A)[2:], hex(B)[2:], hex(C)[2:], hex(D)[2:], hex(E)[2:],hex(F)[2:],hex(G)[2:],hex(H)[2:]) vv = hex(A)[2:].zfill(8) + hex(B)[2:].zfill(8) + hex(C)[2:].zfill(8) + hex(D)[2:].zfill(8) + hex(E)[2:].zfill( 8) + hex(F)[2:].zfill(8) + hex(G)[2:].zfill(8) + hex(H)[2:].zfill(8) return hex((int(vv, 16) ^ int(V, 16)) & (2 ** 512 - 1))[2:] # 扩展函数 def expand(self,B, i): W = [] W_ = [] for i in range(16): W.append(int(B[i * 32:(i + 1) * 32], 2)) for j in range(16, 68): W.append((self.P(W[j - 16] ^ W[j - 9] ^ self.cl(W[j - 3], 15), 1) ^ self.cl(W[j - 13], 7) ^ W[j - 6]) & 0xffffffff) # for j in range(64): # W_.append(hex((W[j]^int(W[j+4]))&0xffffffff)[2:]) for j in range(64): W_.append((W[j] ^ int(W[j + 4])) & 0xffffffff) # for i in range(68): # W[i]=hex(W[i])[2:].zfill(8) return W + W_ def encrypt(self): self.m = self.pad(self.m) B = [] V = [self.iv] n = len(self.m) // 512 for i in range(n): b = self.m[i * 512:(i + 1) * 512] B.append(self.expand(b, i)) print(B) for i in range(n): V.append(self.CF(V[i], B[i])) return V[-1] m='abcd'*16 iv='7380166f4914b2b9172442d7da8a0600a96f30bc163138aae38dee4db0fb0e4e' sm=SM3(m,iv) ss=sm.encrypt() print(ss)
- 作者:Putao0v0
- 链接:https://tangly1024.com/article/SM3%26SM4
- 声明:本文采用 CC BY-NC-SA 4.0 许可协议,转载请注明出处。
相关文章